WireGuard vs OpenVPN: Which VPN Protocol Should You Choose?

The VPN Protocol Decision
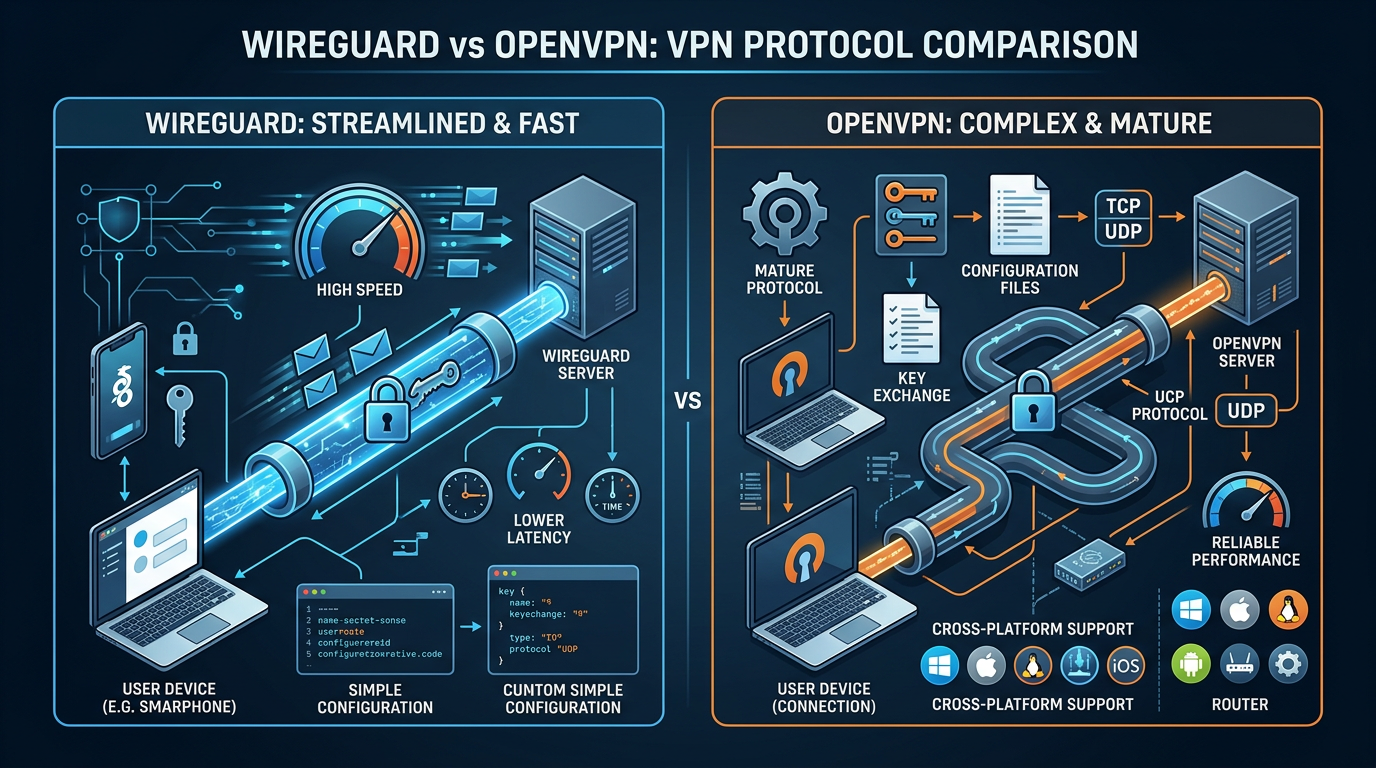
When setting up VPN infrastructure, the choice between WireGuard and OpenVPN isn't just about preference—it affects performance, security posture, and operational complexity. Both protocols encrypt traffic and create secure tunnels, but they take very different approaches.
This comparison helps engineering teams choose the right protocol based on their specific needs: performance requirements, security standards, deployment complexity, and operational overhead.
What Is WireGuard?
WireGuard is a modern VPN protocol designed for simplicity and performance. Released in 2020, it uses state-of-the-art cryptography (ChaCha20, Poly1305, Curve25519, BLAKE2) and runs entirely in the kernel on Linux, resulting in significantly lower latency and higher throughput than traditional VPN protocols.
Key characteristics:
- ~4,000 lines of code (vs OpenVPN's ~100,000+)
- Kernel-space implementation on Linux (faster)
- Modern cryptography by default
- Simple configuration (often a single file)
- Built-in roaming support
What Is OpenVPN?
OpenVPN is the established standard, battle-tested since 2001. It's highly configurable, supports multiple authentication methods, and runs in user space, making it portable across platforms but typically slower than kernel-based solutions.
Key characteristics:
- Mature and widely supported (20+ years)
- Highly configurable (many options)
- User-space implementation (portable, slower)
- Flexible authentication (certificates, passwords, 2FA)
- Extensive documentation and community
Performance Comparison
Speed and Latency
WireGuard typically delivers:
- 2–3x faster throughput than OpenVPN
- Lower latency (especially on Linux)
- Better performance on mobile devices
- Faster connection establishment (~1 second vs 5–10 seconds)
OpenVPN performance:
- Slower but adequate for most use cases
- Higher CPU usage (user-space overhead)
- More latency on initial connection
- Performance varies significantly with configuration
Why it matters: For high-bandwidth applications, remote access with low latency requirements, or mobile users, WireGuard's performance advantage is significant.
Resource Usage
- WireGuard: Lower CPU usage, especially on Linux (kernel implementation)
- OpenVPN: Higher CPU usage, more memory per connection
For teams running VPNs on cost-sensitive infrastructure, WireGuard's efficiency can reduce instance sizes or support more concurrent users.
Security Comparison
Cryptography
WireGuard:
- Modern, audited crypto (ChaCha20-Poly1305, Curve25519)
- Smaller attack surface (less code = fewer vulnerabilities)
- Cryptographic protocol designed from scratch (2015+)
OpenVPN:
- Configurable crypto (can use modern or legacy algorithms)
- Larger codebase (more potential vulnerabilities historically)
- Proven security model (extensively tested over decades)
Both protocols are secure when properly configured. WireGuard's simplicity reduces configuration errors, while OpenVPN's flexibility allows fine-tuning for specific security requirements.
Security Posture
- WireGuard: Secure by default (hard to misconfigure)
- OpenVPN: Security depends heavily on configuration choices
Common OpenVPN misconfigurations that reduce security:
- Weak cipher suites
- Insecure key exchange parameters
- Missing Perfect Forward Secrecy (PFS)
- Improper certificate management
WireGuard avoids these issues by using secure defaults and minimal configuration.
Ease of Use and Configuration
WireGuard Configuration
WireGuard uses a simple, text-based configuration:
[Interface]
PrivateKey = <private-key>
Address = 10.0.0.2/24
[Peer]
PublicKey = <server-public-key>
Endpoint = vpn.example.com:51820
AllowedIPs = 0.0.0.0/0
Advantages:
- Single configuration file
- Easy to understand and audit
- Quick to set up (minutes, not hours)
OpenVPN Configuration
OpenVPN requires multiple files and more complex setup:
# Client config
client
dev tun
proto udp
remote vpn.example.com 1194
ca ca.crt
cert client.crt
key client.key
cipher AES-256-GCM
auth SHA256
Considerations:
- Multiple files (certificates, keys, config)
- More configuration options (can be overwhelming)
- Requires certificate authority (CA) management
- Steeper learning curve
Deployment and Operations
WireGuard Deployment
Pros:
- Fast setup (especially on Linux)
- Minimal dependencies
- Easy to automate (simple config format)
- Built into Linux kernel 5.6+
Cons:
- Less mature tooling ecosystem
- Fewer GUI clients (though improving)
- Limited Windows support (requires driver)
OpenVPN Deployment
Pros:
- Extensive tooling and GUIs
- Cross-platform support (Windows, macOS, Linux, mobile)
- Mature management tools (EasyRSA, commercial solutions)
- Well-documented deployment patterns
Cons:
- More complex initial setup
- Certificate management overhead
- More configuration to maintain
When to Choose WireGuard
Choose WireGuard when:
- Performance is critical (high bandwidth, low latency needs)
- Linux-based infrastructure (kernel support)
- Simplicity matters (smaller team, faster setup)
- Mobile-first use cases
- Modern infrastructure (can adopt newer protocols)
Use cases:
- Site-to-site VPNs between cloud regions
- Remote access for development teams
- High-performance network tunnels
- Mobile workforce VPN
When to Choose OpenVPN
Choose OpenVPN when:
- Cross-platform support is essential (Windows, macOS, legacy systems)
- Complex authentication requirements (2FA, LDAP integration)
- Mature tooling and GUI clients are needed
- Compliance requires specific configurations
- Established infrastructure (already deployed, working well)
Use cases:
- Enterprise VPN with diverse client platforms
- Compliance-driven deployments
- Complex authentication requirements
- Environments requiring extensive customization
Migration Considerations
From OpenVPN to WireGuard:
- Evaluate client support (especially Windows)
- Plan for configuration simplification
- Test performance improvements
- Consider gradual rollout
Staying with OpenVPN:
- Ensure secure configuration (modern ciphers, PFS)
- Regular security updates
- Certificate lifecycle management
- Performance tuning if needed
Conclusion
WireGuard offers superior performance and simplicity for modern, Linux-focused infrastructure. It's the better choice when speed, efficiency, and ease of deployment matter.
OpenVPN remains the right choice for cross-platform deployments, complex authentication needs, and environments requiring extensive customization or mature tooling.
For most engineering teams building new VPN infrastructure today, WireGuard is the default choice unless specific requirements (Windows support, complex auth) dictate otherwise. The performance and operational benefits are significant, and the security model is sound.
Recommendation: Start with WireGuard for new deployments. Use OpenVPN when you need its specific strengths (cross-platform, complex auth, mature tooling).
Construye tu futuro.
¿Listo para transformar tu infraestructura con agentes de IA inteligentes?
Book assessment